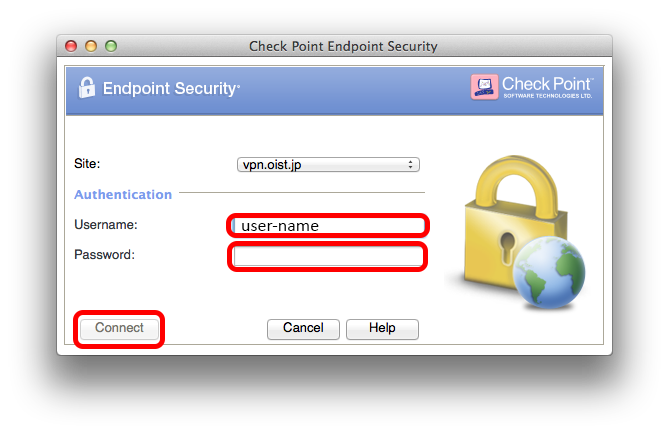
In the Deploymenttab, under Mac Client, click Download. In the window that opens, select which components to include in the package and click Download. If more than one version is in the Package repository, select a client to download. Optional: If Remote Access VPNis part of the package, you can configure a VPN site. Before installing the latest version of Checkpoint Endpoint Security VPN, I have used the uninstaller located in /Library/Applications Support/Checkpoint. I was already looking for files which could be part of the VPN application, but I could find anymore.
Table of Contents:
- Standalone Clients Downloads
- Documentation and Related SecureKnowledge Articles
This release includes support for Standalone E80.71 Endpoint Security VPN client and E80.71 Capsule Docs Mac Clients.
The managed E80.71 Endpoint Security Client for Mac is available with support for FileVault with local users only. Using fileVault with mobile network accounts can lead to deletion of the Personal Recovery Key which in this case can cause data loss. To get the managed Client, contact Check Point Support.
Check Point is working with Apple to solve the FileVault limitation and will update upon resolution.
Notes:
- The relevant links to downloads are located in the relevant section, i.e. Standalone Clients, Utilities/Services.
- The relevant links to documentation are located in the 'Documentation' section.
- It is strongly recommended that you read the E80.71 Endpoint Security Client for Mac Release Notes, before installing this release.
- Also refer to:
- For E80.71 releases for Windows: Refer to sk119676 - Enterprise Endpoint Security E80.71 Windows Clients
Notes:
- The relevant links to downloads are located in the relevant section, i.e., Standalone Clients, Utilities/Services.
- The relevant links to documentation are located in the 'Documentation' section.
- It is strongly recommended that you read the E80.71 Endpoint Security Client for Mac Release Notes, before installing this release.
- Also refer to:
What's New in E80.71 for Mac
Show / Hide this sectionThis release adds these new features:macOS High Sierra (10.13) support for the Endpoint Security client
- 10.13.1 or higher is required.
- macOS High Sierra (10.13) introduces a new feature that requires user approval before loading http://goo.gl/Yq4dYm. This means that to fully activate Endpoint Security, the user must after installing the client, open 'System Preferences > Security & Privacy' and approve system extensions from Check Point.
- After installing the Endpoint Security client blades: Media Encryption, Firewall, and Capsule Docs, this message shows:
System Extension Blocked.
A program tried to load new system extension(s) signed by 'Check Point Software Technologies'. If you want to enable these extensions, open Security & Privacy System Preferences.
New Native Encryption Management
- Encryption management based on FileVault, the native OS encryption from Apple.
- Upgrade gives a seamless migration to the new Native Encryption Management. The disk is encrypted at all times.
- Support for seamless in-place OS upgrade to macOS High Sierra (10.13).
- You can help users recover FileVault-encrypted data if they can’t log in to their Mac. You can help users recover their data or reset their password using a personal recovery key that is unique to the client computer. Alternatively, the administrator can use an institutional recovery key to recover data on a Mac that is deployed with this key.
Remote Access VPN
- Support for Split DNS (disabled by default).
Media Encryption and Media Encryption Offline Tool
Checkpoint Endpoint Security Vpn Client For Mac Download
- Check Point CryptoCore 4.0 is used instead of OpenSSL, which is deprecated by Apple.
- The PKCS#5 PBKDF2-HMAC-SHA256 standard for password based key derivation replaces a proprietary algorithm.
- New encryption progress indicator.
Capsule Docs
- Editing capabilities for protected documents.
- Changing the document protection settings.
- Microsoft Office 2016 support.
- Document expiration support.
- Offline work support.
Standalone Clients Downloads
Show / Hide this sectionNote: These Standalone clients do not require Endpoint Security Server installation as part of their deployment.
E80.71 Standalone Clients
| Platform | Package | Link |
| macOS | E80.71 Endpoint Security VPN for macOS - Disc Image (DMG) | (DMG) |
| E80.71 Endpoint Security VPN for macOS - Automatic Upgrade package (PKG) | (PKG) | |
| E80.71 Endpoint Security VPN for macOS - Signature for automatic upgrade | (signature) |
Capsule Docs E80.71 Clients
| Platform | Package | Link |
| macOS | E80.71 Capsule Docs Mac Editor | (DMG) |
Utilities/Services Downloads
Show / Hide this sectionMedia Encryption Offline Access Tool E80.71 for macOS
| Platform | Package | Link |
| macOS | E80.71 Media Encryption Offline Access Tool | (DMG) |
Documentation and Related SecureKnowledge Articles
Show / Hide this section| Document |
| E80.71 Endpoint Security Client for Mac |
| E80.71 Endpoint Security Client for Mac Release Notes |
| Remote Access VPN Clients |
| E80.71 Endpoint Security VPN Clients for Mac Release Notes |
| E80.71 Endpoint Security VPN for Mac Administration Guide |
| Capsule Docs Client |
| E80.71 Capsule Docs Plugin User Guide |
For more information on Check Point releases see: Maintrain Release map, Maintrain Upgrade map, Maintrain Backward Compatibility map, Maintrain Releases plan.
For more information on the Enterprise Endpoint Security E80.71 Client, see:
- For installation and upgrade instructions, use the procedures in: Installation and Upgrade Guide for Gaia Platforms R77 Versions
For more information on Check Point releases see: Maintrain Release map, Maintrain Upgrade map, Maintrain Backward Compatibility map, Maintrain Releases plan.
For more information on the Enterprise Endpoint Security E80.71 Client, see:

- For installation and upgrade instructions, use the procedures in: Installation and Upgrade Guide for Gaia Platforms R77 Versions
Revision History
Show / Hide this section| Date | Description |
| 15 July 2019 | Link to Maintrain Release map was replaced |
| 29 Jan 2018 | VPN Standalone client builds were replaced due to addressing a connectivity issue which was introduced as a result of macOS High Sierra 10.13.2 January Supplemental update. |
| 18 Dec 2017 | First release of this document. |
Check Point Remote Access Solutions
In This Section: |
Secure Remote Access
In today's business environment, it is clear that workers require remote access to sensitive information from a variety of locations and a variety of devices. Organizations must also make sure that their corporate network remains safe and that remote access does not become a weak point in their IT security.
Checkpoint Endpoint Security Vpn Client Macos
This chapter:

- Gives you information about Check Point's secure remote access options.
- Helps you decide which remote access client or clients best match your organization's requirements.
- Shows you where to get more information.
Types of Solutions
All of Check Point's Remote Access solutions provide:
- Enterprise-grade, secure connectivity to corporate resources.
- Strong user authentication.
- Granular access control.
Factors to consider when choosing remote access solutions for your organization:
- Client-Based vs. Clientless - Does the solution require a Check Point client to be installed on the endpoint computer or is it clientless, for which only a web browser is required. You might need multiple solutions within your organization to meet different needs.
- Secure Connectivity and Endpoint Security - Which capabilities does the solution include?
- Secure Connectivity - Traffic is encrypted between the client and VPN gateway. After users authenticate, they can access the corporate resources that are permitted to them in the access policy. All Check Point solutions supply this.
- Endpoint Security - Endpoint computers are protected at all times, even when there is no connectivity to the corporate network. Some Check Point solutions supply this.
Client-Based vs. Clientless
Check Point remote access solutions use IPsec and SSL encryption protocols to create secure connections. All Check Point clients can work through NAT devices, hotspots, and proxies in situations with complex topologies, such as airports or hotels. These are the types of installations for remote access solutions:
- Client-based - Client application installed on endpoint computers and devices. The client supplies access to most types of corporate resources according to the access privileges of the user.
- Clientless - Users connect through a web browser and use HTTPS connections. Clientless solutions usually supply access to web-based corporate resources.
- On demand client - Users connect through a web browser and a client is installed when necessary. The client supplies access to most types of corporate resources according to the access privileges of the user.
Secure Connectivity and Endpoint Security
You can combine secure connectivity with additional features to protect the network or endpoint computers.
- Secure Connectivity - Traffic is encrypted between the client and VPN gateway and strong user authentication is supported. All Check Point solutions supply this.
These solutions require licenses based on the number of users connected at the same time.
- Security Verification for Endpoint computers - Makes sure that devices connecting to the gateway meet security requirements. Endpoint machines that are not compliant with the security policy have limited or no connectivity to corporate resources. Some Check Point solutions supply this.
- Endpoint Security:
- Desktop Firewall - Protects endpoint computers at all times with a centrally managed security policy. This is important because remote clients are not in the protected network and traffic to clients is only inspected if you have a Desktop Firewall. Some Check Point solutions supply this
- More Endpoint Security Capabilities - Check Point solutions can include more Endpoint Security capabilities, such as anti-malware, disk encryption and more.
These solutions require licenses based on the number of clients installed.
Remote Access Solution Comparison
Details of the newest version for each client and a link for more information are in sk67820.
Checkpoint Endpoint Security Vpn Client For Mac Os
SSL VPN Portal and Clients
Name | Supported Operating Systems | Client or Clientless | Encryption Protocol | Security Verification for Endpoint Devices | Desktop Firewall on Endpoint Devices | IPv6 Support |
|---|---|---|---|---|---|---|
Mobile Access Web Portal | Windows, Linux, Mac OS, iOS, Android | Clientless | SSL | R77.10 and higher | ||
SSL Network Extender for Mobile Access Blade | Windows, Linux, Mac OS | On-demand Client through Mobile Access Portal) | SSL | |||
Capsule Workspace for iOS (previously Mobile Enterprise) | iOS | Client | SSL | Jailbreak & Root Detection MDM Cooperative Enforcement (sk98201) | R77.10 and higher | |
Capsule Workspace for Android (previously Mobile Enterprise) | Android | Client | SSL | Jailbreak & Root Detection MDM Cooperative Enforcement (sk98201) | R77.10 and higher |
Layer-3 VPN Tunnel Clients
Name | Supported Operating Systems | Client or Clientless | Encryption Protocol | Security Verification for Endpoint Devices | Desktop Firewall on Endpoint Devices | IPv6 Support |
|---|---|---|---|---|---|---|
Capsule Connect for iOS (previously Mobile VPN) | iOS | Client | IPsec / SSL | MDM Cooperative Enforcement (sk98201) | ||
Capsule VPN for Android (previously Mobile VPN) | Android | Client | IPsec/SSL | MDM Cooperative Enforcement (sk98201) | ||
Check Point VPN Plugin for Windows 8.1 | Windows 8.1 | Pre- installed client | SSL | |||
Check Point Mobile for Windows | Windows | Client | IPsec |
Layer-3 VPN Tunnel Clients Integrated with Endpoint Security
Name | Supported Operating Systems | Client or Clientless | Encryption Protocol | Security Verification for Endpoint Devices | Desktop Firewall on Endpoint Devices | IPv6 Support |
|---|---|---|---|---|---|---|
Endpoint Security VPN for Windows | Windows | Client | IPsec | |||
Endpoint Security VPN for Mac | Mac OS | Client | IPsec | |||
Endpoint Security Suite Remote Access VPN Blade | Windows, Mac OS | Client | IPsec |
Additional Remote Access Solutions
Name | Supported Operating Systems | Client or Clientless | Encryption Protocol | Security Verification for Endpoint Devices | Desktop Firewall on Endpoint Devices | IPv6 Support |
|---|---|---|---|---|---|---|
SecuRemote | Windows | Client | IPsec | |||
Check Point GO VPN | Windows | Clientless - Requires a Check Point GO device | SSL |
Summary of Remote Access Options
Below is a summary of each Remote Access option that Check Point offers. All supply secure remote access to corporate resources, but each has different features and meets different organizational requirements.
Details of the newest version for each client and a link for more information are in sk67820.
SSL Network Extender
SSL Network Extender is a thin SSL VPN on-demand client installed automatically on the user's machine through a web browser. It supplies access to all types of corporate resources.
SSL Network Extender has two modes:
- Network Mode - Users can access all application types (Native-IP-based and Web-based) in the internal network. To install the Network Mode client, users must have administrator privileges on the client computer.
Supported Platforms: Windows, Mac OS X, Linux
- Application Mode - Users can access most application types (Native-IP-based and Web-based) in the internal network, including most TCP applications. The user does not require administrator privileges on the endpoint machine.
Supported Platforms - Windows
Required Licenses - Mobile Access Software Blade on the gateway
Where to Get the Client - Included with the Security Gateway. See sk67820.
Capsule Workspace for iOS
Capsule Workspace for iOS is an SSL VPN client. It supplies secure connectivity and access to web-based corporate resources and Microsoft Exchange services. It also gives secure access to Capsule Docs protected documents It was previously called Mobile Enterprise.
Capsule Workspace is ideal for mobile workers who have privately-owned smart phones or tablets. It protects only the business data inside the App and does not require device-level security measures, such as device-lock or device-wipe.
Required Licenses - Mobile Access Software Blade on the gateway
Supported Platforms - iOS
Where to Get the Client - Apple App Store
Capsule Workspace for Android
Capsule Workspace for Android is an SSL VPN client. It supplies secure connectivity and access to web-based corporate resources and Microsoft Exchange services. It also gives secure access to Capsule Docs protected documents. It was previously called Mobile Enterprise.
Capsule Workspace for Android is ideal for mobile workers who have privately-owned smart phones or tablets. It protects only the business data inside the App and does not require device-level security measures, such as device-lock or device-wipe.
Required Licenses - Mobile Access Software Blade on the gateway
Supported Platforms - Android
Where to Get the Client - Google Play Store
Capsule Connect for iOS
Capsule Connect is a full L3 tunnel app that gives users network access to all mobile applications. It supplies secure connectivity and access to all types of corporate resources. It was previously called Mobile VPN.
Required Licenses - Mobile Access Software Blade on the gateway
Supported Platforms - iOS 6.0 +
Where to Get the Client - Apple App Store
Capsule VPN for Android
Capsule VPN for Android devices is an L3 VPN client. It supplies secure connectivity and access to corporate resources using L3 IPSec/SSL VPN Tunnel. It was previously called Mobile VPN.
Required Licenses - Mobile Access Software Blade on the gateway
Supported Platforms - Android 4 + (ICS+)
Where to Get the Client - Google Play Store
Check Point VPN Plugin for Windows 8.1
Check Point VPN Plugin for Windows 8.1 is an L3 VPN client. It supplies secure connectivity and access to corporate resources using L3 SSL VPN Tunnel.
Required Licenses - Mobile Access Software Blade on the gateway
Supported Platforms - Windows 8.1
Where to Get the Client - Pre-installed with Windows.
Check Point Mobile for Windows
Check Point Mobile for Windows is an IPsec VPN client. It is best for medium to large enterprises that do not require an Endpoint Security policy.
The client gives computers:
- Secure Connectivity
- Security Verification
Required Licenses - IPsec VPN and Mobile Access Software Blades on the gateway.
Supported Platforms - Windows
Where to Get the Client - Check Point Support Center - sk67820.
Endpoint Security VPN
Endpoint Security VPN is an IPsec VPN client that replaces SecureClient. It is best for medium to large enterprises.
The client gives computers:
Checkpoint Endpoint Security Vpn Client For Mac Catalina
- Secure Connectivity
- Security Verification
- Endpoint Security that includes an integrated Desktop Firewall, centrally managed from the Security Management Server.

Required Licenses - The IPsec VPN Software Blade on the gateway, an Endpoint Container license, and an Endpoint VPN Software Blade license on the Security Management Server.
Supported Platforms - Windows
Where to Get the Client - Check Point Support Center - sk67820.
Note - Endpoint Security VPN on Mac OS X includes a Desktop Firewall but not Security Verification. |

Endpoint Security VPN for Mac
Endpoint Security VPN combines Remote Access VPN with Endpoint Security in a client that is installed on endpoint computers. It is recommended for managed endpoints that require a simple and transparent remote access experience together with Desktop Firewall rules. It includes:
- Enterprise Grade Remote Access Client that replaces SecureClient for Mac.
- Integrated Desktop Firewall, centrally managed from the Security Management Server.
Required Licenses - The IPsec VPN Software Blade on the gateway, an Endpoint Container license, and an Endpoint VPN Software Blade license on the Security Management Server.
Supported Platforms for Users - Mac OS X
Where to Get the Client - Check Point Support Center - sk67820.
Endpoint Security Suite
The Endpoint Security Suite simplifies endpoint security management by unifying all endpoint security capabilities in a single console. Optional Endpoint Security Software Blades include: Firewall, Compliance Full Disk Encryption, Media Encryption & Port Protection, and Anti- Malware & Program Control. As part of this solution, the Remote Access VPN Software Blade provides full, secure IPsec VPN connectivity.
The Endpoint Security suite is best for medium to large enterprises that want to manage the endpoint security of all of their endpoint computers in one unified console.
Required Licenses - Endpoint Security Container and Management licenses and an Endpoint VPN Software Blade on the Security Management Server.
Supported Platforms - Windows, Mac OS X
Where to Get the Client - Check Point Support Center - sk67820.
SecuRemote
SecuRemote is a secure, but limited-function IPsec VPN client. It provides secure connectivity.
Required Licenses - IPsec VPN Software Blade on the gateway. It is a free client and does not require additional licenses.
Supported Platforms - Windows
Where to Get the Client - Check Point Support Center - sk67820.
Check Point GO
Check Point GO is a portable workspace with virtualized Windows applications, on a secure and encrypted USB Flash Drive. Users insert the USB device into a host PC and securely access their workspace and corporate resources through SSL VPN technology.
Check Point GO is ideal for mobile workers, contractors, and disaster recovery. The virtual workspace is segregated from the host PC and controls the applications and data that can run in Check Point GO.
It provides:
Check Point Endpoint Security Vpn Client Mac
- Secure Connectivity
- Security Verification
Checkpoint Endpoint Security Vpn Client For Mac Windows 10
Required Licenses - IPsec VPN Software Blade on the gateway and Check Point GO devices.
Supported Platforms - Windows
Where to Get the Client - Check Point Support Center - sk67820.
